Booking.com confirms customer data access. Here's why Australian businesses should care.
Booking.com said hackers may have accessed customer names, email addresses, phone numbers, and booking information. That kind of travel data can be turned into highly believable phishing and impersonation attacks against Australian businesses, especially around finance, executive support, and staff on the move.
Source: TechCrunch, April 13, 2026

Reported Access
Names, email addresses, phone numbers, and booking information
Why It Matters
Travel context makes phishing and impersonation messages far more convincing.
Business Risk
Invoice fraud, Microsoft 365 compromise, and executive support targeting.
Booking.com has confirmed that hackers may have accessed customer details including names, email addresses, phone numbers, and booking information. On the surface, that sounds like a travel-platform story. For Australian businesses, it is much bigger than that.
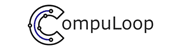
Travel-related data is incredibly useful to cybercriminals because it adds context. If an attacker knows who is travelling, where they are booked, and when they are expected to arrive, they can build fake messages that look far more convincing than a generic scam email. That shifts the risk from ordinary spam to targeted impersonation.
What happened in the Booking.com breach?
According to TechCrunch, Booking.com said hackers may have accessed customer names, email addresses, phone numbers, and booking details. Even without card data, that information can still be used to send fake reservation updates, bogus refund messages, false payment notices, and hotel-themed phishing lures that line up with a real trip.
That is why this incident should not be brushed off as a consumer-only privacy issue. Travel data can be weaponised quickly.
Why this should matter to Compuloop clients
If your staff travel for conferences, interstate meetings, customer visits, executive roadshows, or project deployments, this kind of breach can create direct business exposure. It can also hit finance teams and executive assistants who handle bookings and reimbursements on behalf of others.
How the breach affects Australian businesses
Australian organisations often manage travel through shared inboxes, delegated approvals, and quick coordination between staff on the road and people back in the office. That creates a perfect opening for attackers when a message looks specific enough to feel real.
Imagine a finance manager receives a payment update tied to an actual executive trip. Imagine an assistant gets a fake hotel notice referencing the right city and check-in date. Imagine a travelling employee receives a reservation issue message while standing in an airport queue. Those are exactly the kinds of moments where attackers win.
The fallout can include fraudulent payment requests, credential theft through fake Microsoft 365 login pages, impersonation of hotel staff, and compromise of internal email threads.
Why travel booking data is so useful to attackers
Attackers do not always need to steal money straight away. Sometimes they just need a believable pretext. Travel data gives them that. It helps them craft emails and text messages that refer to real bookings, real dates, and real destinations. That makes phishing harder to spot and far more dangerous.
If the targeted person works in finance, leadership, or executive support, the risk goes further. One compromised account can turn into invoice fraud, internal impersonation, or access to broader Microsoft 365 conversations. That is why businesses need to think about identity security and process controls, not just staff awareness.
What businesses should be watching for now
- Travel or payment messages that create urgency
- Links asking staff to re-enter passwords or card details
- Requests to pay outside normal channels
- Hotel or booking notices that reference real trips
- Unusual approval requests tied to employee travel
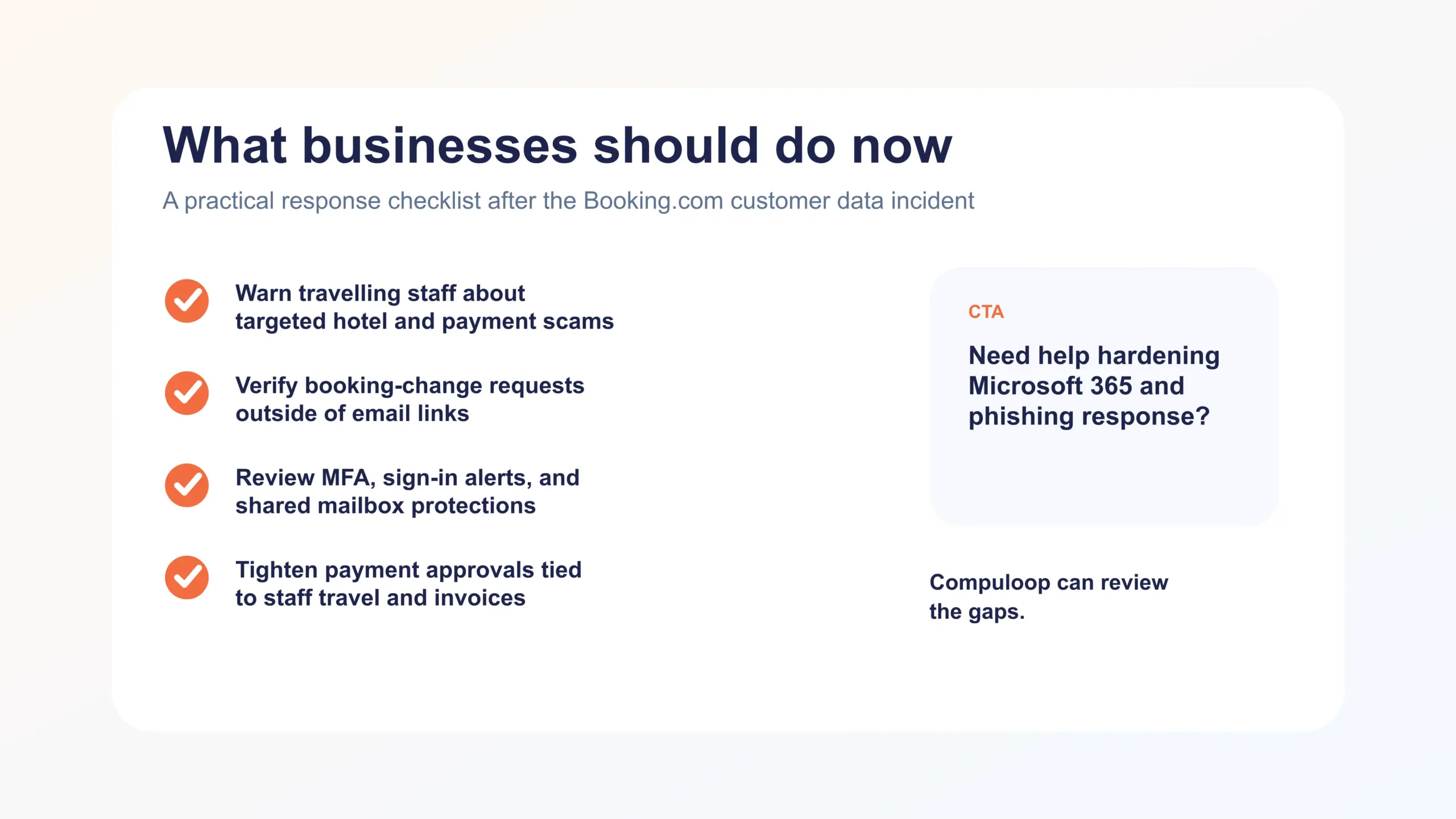
What Australian businesses should do next
This is the time for practical action, not a generic awareness email and a shrug. If your team uses Booking.com or similar platforms for business travel, review the controls around identity, email, approvals, and shared inboxes now.
- Warn travelling staff, executive assistants, and finance teams about travel-themed phishing.
- Verify booking changes and payment requests directly rather than through links in email or SMS.
- Review Microsoft 365 protections, especially MFA and suspicious sign-in alerts.
- Check whether shared mailboxes and finance accounts are better protected than standard users.
- Audit payment approval steps for hotel and travel-related expenses.
- Make sure your backup and response process is clear if an account is compromised.
The bigger lesson
This breach is a reminder that attackers do not always need to break into your business first. Sometimes they use someone else’s data leak to get around your defences. That is why Australian businesses should be looking hard at phishing resistance, identity security, approval processes, and how quickly suspicious travel-related messages get escalated.
If your business needs help tightening phishing resilience, hardening Microsoft 365, or reducing impersonation risk, Compuloop’s CyberSecurity Australia and Business IT Support services are directly relevant here.
Sources and external guidance
TechCrunch coverage of the Booking.com breach, Booking.com support guidance, and ACSC scam and phishing advice are worth reviewing if your staff travel regularly for work.
Quick take
This is not just travel-sector noise. It is a live phishing and impersonation risk for Australian businesses with travelling staff.
Focus keyphrase: Booking.com breach Australian businesses
Internal links in this story
Need help now?
If you want a practical review of your phishing exposure, Microsoft 365 controls, or payment approval weak points, Compuloop can help map the gaps before attackers do.
Turn breach headlines into a security review before they turn into incidents.
Compuloop helps Australian businesses harden Microsoft 365, strengthen phishing resistance, lock down approvals, and respond faster when targeted scams start landing.