Rockstar Games is back in the cyber spotlight, this time over a breach the company says was tied to a third party rather than a direct hit on its own frontline systems.
As of April 14, 2026, Rockstar has confirmed that a limited amount of internal company information was accessed in connection with a third-party data breach. On the surface, that sounds contained. Underneath it, though, is the part business owners should pay attention to.
The latest cyber security breach in the headlines is another reminder that companies are no longer just defending laptops, servers, and staff logins. They are defending every outside platform plugged into the business, every analytics tool, every cloud connection, and every token quietly sitting between systems.

Rockstar said the exposed information was a limited amount of non-material company information and added that the incident had no impact on the organisation or its players. Even so, the case has landed in the middle of cyber security news because of the route attackers allegedly took. Reports indicate the threat actors tied the intrusion to Anodot, a cloud analytics and monitoring platform, and claimed the exposure involved data in a Snowflake cloud environment.
That is what makes this more than another breach headline. It pushes a familiar problem back into view: the weak point is often not the company at the centre of the story, but the service provider sitting two steps behind it.
From a newsroom chair, the pattern is hard to miss. The company name changes. The technology stack changes. The script keeps coming back. A trusted platform is compromised, access material is abused, and the customer ends up wearing the public fallout.
What happened in the latest cyber security breach?
According to reporting published on April 13, 2026, the ShinyHunters cybercrime group claimed responsibility for breaching systems linked to Rockstar Games and threatened to leak stolen data if its demands were not met. Rockstar later confirmed that some company data had been accessed in connection with a third-party breach, while downplaying the operational impact.
The detail that deserves the most attention is the alleged attack path. Reports say attackers may have obtained authentication tokens tied to a third-party platform, allowing access to customer cloud environments without directly breaching every victim one by one. If that account holds up, it is a clean example of how cloud breaches spread now: not always by battering down the front door, but by slipping through a trusted side entrance.
For Australian organisations, this is not just entertainment-industry drama playing out offshore. Plenty of local businesses rely on managed cloud stacks, reporting tools, SaaS dashboards, outsourced monitoring, and productivity platforms stitched together with privileged connections. That convenience saves time, but it also widens the blast radius when one supplier gets hit.
Why this breach matters beyond Rockstar Games
The bigger story here is how modern attacks travel sideways.
Attackers do not always need to break your front door if they can borrow a key from someone already inside the building. That key might be an exposed token, an over-permissioned service account, an old API secret, or a monitoring integration no one has reviewed in months.
For many businesses, especially small and mid-sized organisations, third-party exposure is where risk becomes harder to see. Internal teams may be patching endpoints, enforcing MFA, and investing in secure backups while overlooking one plain fact: a supplier with broad access can still open the path to sensitive data.

That is why this latest cyber security breach story should resonate with business owners, directors, and operations teams, not just CISOs. If your company uses cloud billing tools, analytics services, cost-monitoring platforms, Microsoft 365 integrations, or external IT providers, then supplier access is part of your attack surface whether you think about it every day or not.
The practical fallout is simple enough. A breach that starts in one platform can quickly turn into data exposure, reputational damage, legal and contractual headaches, incident response costs, customer trust erosion, and forced credential resets with service disruption.
The cyber security lessons Australian businesses should take from this
This latest cyber security breach should push companies to ask a few uncomfortable questions straight away.
First, who has access to your cloud environment today through third-party tooling? Not who had access last quarter on paper. Who has access right now.
Second, how many tokens, keys, service accounts, and app-to-app connections could be used to pivot into business systems if a supplier were compromised?
Third, if one of your software providers called tomorrow and said they had suffered a breach, would you know exactly what to disable, rotate, isolate, or monitor first?
Too many businesses still treat third-party security like a procurement checkbox. In reality, it needs to sit inside day-to-day operations. Vendor reviews should not stop after onboarding. Access should be limited to what is actually needed. Old credentials should be rotated. Logs should be retained. Shared secrets should not live forever. And any trusted connection should be treated as something that may eventually be tested.
There is also a communication lesson buried in this one. Rockstar moved quickly to confirm the incident and tamp down speculation around impact. That matters. In a breach, silence creates its own mess. Fast, accurate, measured communication can stop a security incident from turning into a trust problem as well.
What businesses should do next
If this latest cyber security breach feels familiar, it is because the same themes keep resurfacing across industries. Entertainment, healthcare, government, finance, logistics, and professional services are all running into versions of the same problem: too many interconnected systems, too much inherited trust, and not enough visibility into how third-party access is really controlled.
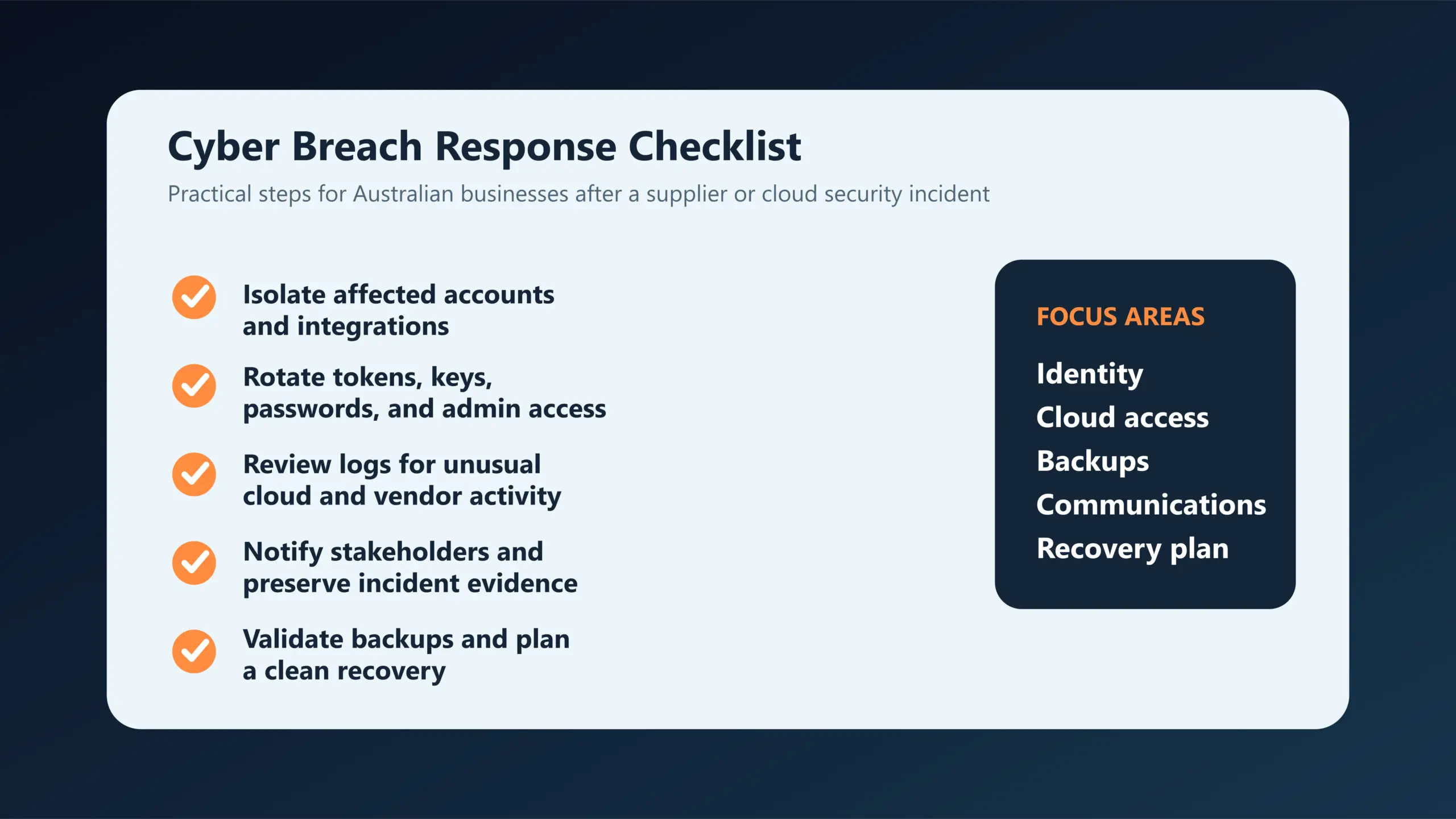
For Australian businesses, the response should be practical rather than panicked:
- Review every third-party platform with access to cloud or production data.
- Rotate exposed or aging API keys, tokens, and service credentials.
- Enforce MFA and conditional access everywhere it can be applied.
- Limit vendor permissions to the minimum required.
- Maintain immutable, tested backups.
- Monitor logs for unusual access from integrated services.
- Build an incident response checklist that includes supplier-driven breaches.
For organisations that want to tighten that posture, this is the right moment to strengthen internal resilience with managed monitoring, identity hardening, secure cloud configuration, and tested recovery planning. Compuloop already speaks directly to those needs through its CyberSecurity Australia service, Microsoft Modern Workplace support, and Data Backup Solutions.
Final word
The latest cyber security breach involving Rockstar Games may not be the biggest breach of the year. It may not end up being the most damaging either. But it is one of the clearest recent examples of how modern attacks work in the real world.
- They follow trust.
- They follow integrations.
- They follow convenience.
And when businesses watch the systems but not the links between them, attackers do not need to force their way in. They take the path that is already open.
That is the warning in this latest cyber security breach story, and Australian businesses would be smart not to shrug it off.
FAQ: Latest cyber security breach
What is the latest cyber security breach in the news?
As of April 14, 2026, one of the latest confirmed high-profile incidents involves Rockstar Games, which confirmed that limited company information was accessed in connection with a third-party data breach.
Was Rockstar Games directly hacked?
Public reporting indicates the incident was connected to a third-party cloud analytics breach rather than a simple direct compromise of Rockstar’s own systems. Rockstar confirmed data access but said the impact was limited.
Why does this breach matter for small businesses?
Because it shows how third-party software, cloud integrations, and authentication tokens can expose business data even when the original compromise begins outside your own company.
How can businesses reduce third-party breach risk?
Businesses should limit vendor access, rotate credentials regularly, enforce MFA, monitor cloud logs, review integrations, and maintain tested backups and incident response plans.
Source: Reporting from The Record, published April 13, 2026.