For plenty of Australian businesses, cyber security still gets treated as something to sort out later.
Then later arrives fast. A phishing email gets through. Someone opens a fake invoice. A remote login is reused. A server misses a patch. The conversation shifts from we should tighten this up to how bad is this going to be?
That is exactly why the Essential Eight matters.
The Essential Eight is not some abstract security checklist built only for giant enterprise teams. It is a practical baseline developed by the Australian Signals Directorate and explained by the Australian Cyber Security Centre to make common attacks harder to pull off. For Australian businesses trying to lower risk without getting buried in jargon, that is why it matters.

Put simply, the Essential Eight is a set of eight mitigation strategies designed to protect internet-connected systems. The ACSC treats it as a baseline, not a silver bullet. That matters. It will not stop every incident, but it does make common attacks harder to land and harder to spread.
What is the Essential Eight?
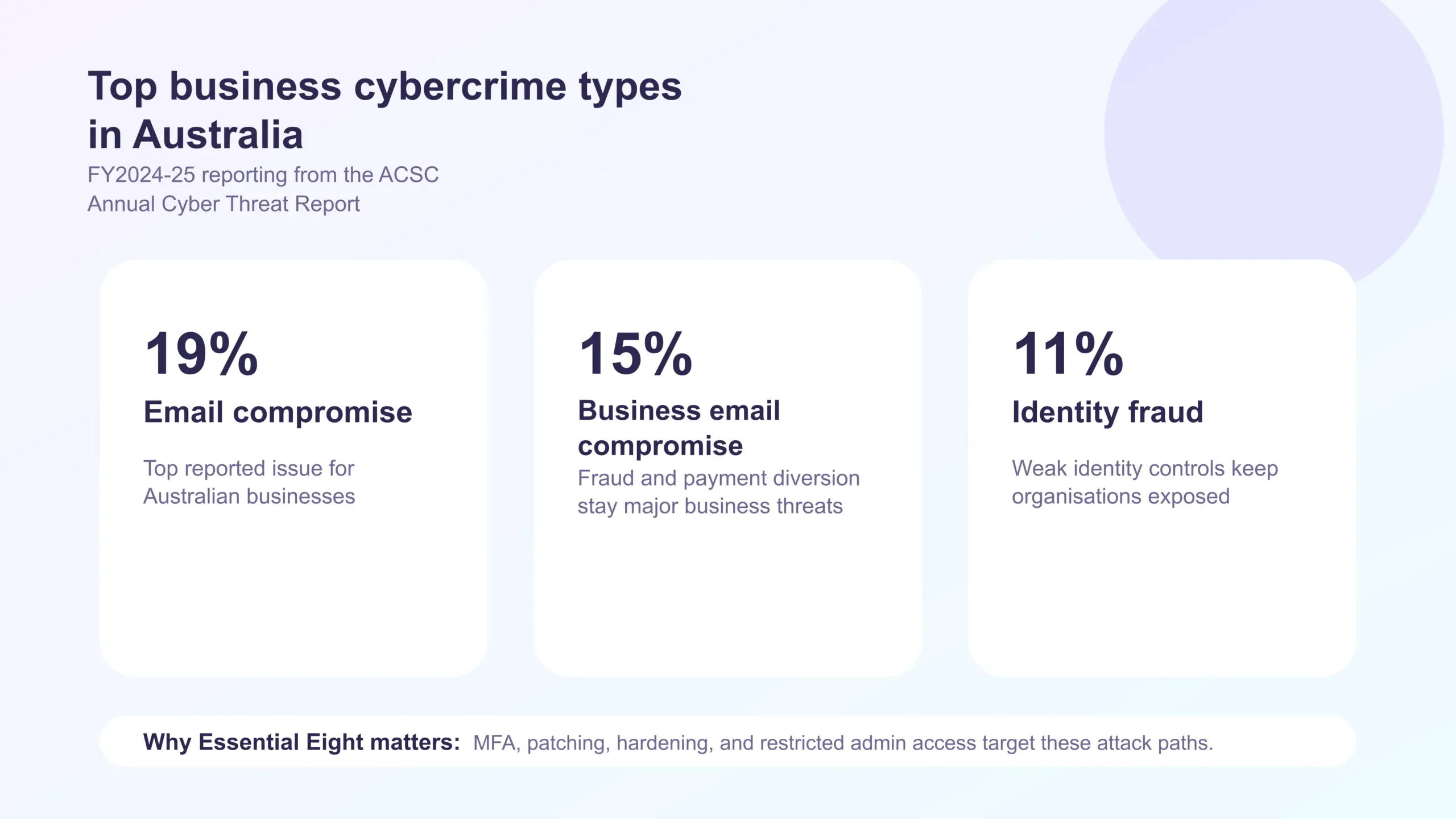
According to the ACSC, the Essential Eight consists of application control, patching applications, configuring Microsoft Office macro settings, user application hardening, restricting administrative privileges, patching operating systems, multi-factor authentication, and regular backups.
On paper, that list looks simple. In practice, it covers the same weak points attackers keep exploiting every day: unpatched software, too much admin access, weak identity controls, risky document settings, and poor recovery planning.
What makes the ACSC guidance useful is that it does not stop at naming the controls. It also sets out a maturity model, so businesses can improve over time instead of pretending everything gets fixed in one sprint.
That is a much more honest way to approach security.
Why the Essential Eight matters for Australian businesses
One of the biggest mistakes small and mid-sized businesses make is assuming this framework is only for government or heavily regulated environments.
It is not.
The Essential Eight matters for Australian businesses because most businesses face the exact kinds of threats it is meant to reduce. These are not exotic attacks. They are the everyday hits aimed at inboxes, remote access portals, Microsoft 365 tenants, browsers, endpoints, and cloud-connected systems.
That includes phishing and credential theft, ransomware, malicious Office documents, exploitation of known vulnerabilities, abuse of admin accounts, and business disruption after data loss or encryption.
If your business runs on email, cloud apps, shared files, web browsers, staff laptops, remote support tools, and line-of-business software, then the Essential Eight is relevant to you.
It is also relevant because the cost of good enough security keeps rising. One incident can mean downtime, recovery costs, legal headaches, cyber insurance issues, customer trust damage, and weeks of disruption. For many businesses, the real question is whether they can absorb the hit when basic controls are missing.
The practical value of each control
One reason the Essential Eight has stuck around is that each control solves a practical problem.
Application control is about stopping unauthorised code from running. That matters because if the wrong executable, script, or payload cannot run, many attacks lose momentum quickly.
Patching applications and operating systems comes down to speed and discipline. The ACSC has put strong emphasis on urgent patching, especially where critical vulnerabilities or working exploits exist. Attackers do not wait while internal teams debate maintenance windows.
Restricting Microsoft Office macros and hardening user applications targets the tools staff use every day. Attackers know users live inside email, documents, browsers, and PDFs. That is why so many attacks start there.
Restricting administrative privileges deals with a problem that quietly makes everything worse: too much access in too many hands. If a privileged account is compromised, the damage grows quickly.
Multi-factor authentication helps stop stolen credentials from becoming a full compromise. It is not perfect, but it is still one of the most valuable friction points a business can add.
Regular backups are your recovery safety net. They do not prevent an attack, but they can determine whether a business returns to operation in hours, days, or not at all.
Taken together, these controls work better as a group than as isolated fixes. That is one of the ACSC’s strongest points: the Essential Eight is designed so the controls complement one another.
Why Australian businesses should care about the maturity model
A lot of businesses get stuck because they treat security like a pass-fail exercise. Either you are secure or you are not. Either you have the policy or you do not.
The Essential Eight maturity model is more useful than that.
It gives businesses a way to improve in stages. Instead of pretending everything can be done at once, leadership teams can decide what maturity level makes sense for their environment, plan the work, reduce exceptions, and move forward deliberately.
That risk-based approach is important because not every business has the same systems, staffing, compliance obligations, or exposure. A growing professional services firm in Sydney will not look identical to a manufacturer, a healthcare provider, or a multi-site retailer. But they all still need a structured baseline.
The model also forces a more honest question: where are the gaps right now?
Not the gaps in policy documents.
The gaps in live systems, admin rights, patch cadence, MFA coverage, backups, and hardening controls.
That is where real security work starts.
Where many businesses go wrong
Plenty of Australian businesses say they are aligned to the Essential Eight when what they really mean is they have started a few pieces of it.
That is not the same thing.
Common gaps include MFA rolled out for some users but not all critical services, backups in place but not regularly tested for recovery, local admin still enabled across endpoints, patching delayed because ownership is unclear, macros controlled in policy but not enforced technically, and security tools installed but not hardened or monitored properly.
This is where the framework becomes useful as a reality check. It pushes businesses beyond surface-level confidence and into measurable implementation.
Why the Essential Eight is also a business conversation
It is easy to treat the Essential Eight as a pure IT responsibility. That view is too narrow.
This is also a leadership, operations, and business continuity issue.
If key staff lose access, if shared systems go offline, if client data is exposed, or if the business cannot recover cleanly from ransomware, the impact does not stay inside the IT team. It lands across the whole organisation.
That is why Australian businesses need to look at the Essential Eight through the lens of resilience, not just compliance or technical hygiene.
It helps answer questions like how easy it is for an attacker to move through the environment, how much damage one compromised account could do, how fast the business could recover if something breaks badly, and whether trust is being assumed where controls should be enforced.
Those are not just cyber questions. They are business survival questions.
What businesses should do next
If the Essential Eight has been sitting on the we should get to that list, now is the time to stop treating it as background reading.
Start with a practical review:
- Assess where your current controls actually stand.
- Identify which of the eight are partially implemented, missing, or inconsistent.
- Decide on a realistic target maturity level.
- Prioritise the highest-risk gaps first.
- Reduce exceptions rather than normalising them.
- Test your recovery process, not just your backups.

For many organisations, this is also the point where outside help can be useful. Not because the framework is impossible to understand, but because implementation often stalls when nobody owns the whole picture.
If your business needs help reviewing its controls, strengthening endpoint and identity protections, tightening Microsoft 365 security, or improving backup and recovery posture, Compuloop’s CyberSecurity Australia services, Business IT Support, and Data Backup Solutions are directly relevant to that work.
Final word
The Essential Eight matters because it deals with the basics that still break businesses when they are ignored.
It gives Australian businesses a practical security baseline.
It gives leadership teams a clearer way to measure progress.
And it gives attackers fewer easy wins.
That is the real value here. Not theory. Not security theatre. Just fewer open doors, better recovery options, and a stronger operating environment when something eventually gets tested.
For Australian businesses, that is no longer optional.
FAQ: Essential Eight for Australian businesses
What is the Essential Eight in Australia?
The Essential Eight is a set of eight mitigation strategies developed by the Australian Signals Directorate and explained by the ACSC to help organisations reduce the risk of common cyber attacks.
Is the Essential Eight only for government agencies?
No. While it is widely used in government and regulated environments, the ACSC guidance is highly relevant for private businesses as well, especially those relying on internet-connected systems and cloud services.
What is the best Essential Eight maturity level for businesses?
There is no single target that suits every organisation. The ACSC recommends using a risk-based approach and working toward a maturity level that fits the environment and threat profile.
Why is the Essential Eight important for small and medium businesses?
Because it focuses on practical controls that reduce the likelihood and impact of common attacks such as phishing, ransomware, exploitation of known vulnerabilities, and credential theft.
Sources: ACSC Essential Eight, Essential Eight maturity model and ISM mapping, and the Essential Eight maturity model FAQ.